
Do You Need Penetration Testing?
What is Penetration Testing?
Penetration testing or pen testing is a security exercise where a cyber-security expert attempts to find and exploit vulnerabilities in a system, application, or network device. The purpose of this simulated attack is to identify any weak spots in a system’s defenses that attackers could take advantage of.
This is like a bank hiring someone to dress as a burglar and try to break into their building and gain access to the vault. If the ‘burglar’ succeeds and gets into the bank or the vault, the bank will gain valuable information on how they need to tighten their security measures.
Our Security Risk Assessment protocol is tailored to client objectives, as well as the size, scale, and type of organization. It can explore controls of various security standards and incorporate a review of controls required by various regulatory requirements.
InData brings years of experience in assessing information security risk across multiple sectors, including the Motion Picture Association of America (MPAA), agriculture, financial services, pharmaceutical, health providers, government, and other industries.
Who Performs a Penetration Test?
It’s best to have a pen test performed by someone with little-to-no prior knowledge of how the system is secured because they may be able to expose blind spots in the infrastructure. For this reason, outside vendors specializing in these tasks, much like InData, are usually brought in to perform the tests. These engineers are often referred to as ‘ethical hackers’ since they are being hired to hack into a system with permission and for the purpose of increasing security and all-around protection.
Many ethical hackers are extremely experienced system administrators, network engineers, system architects, and developers with advanced certifications for penetration testing. At the same time, some of the best ethical hackers are self-taught. In fact, some are reformed criminal hackers who now use their expertise to help fix security flaws rather than exploit them. The best candidate to carry out a vulnerability test can vary greatly depending on the target company and what type of test they want to initiate.
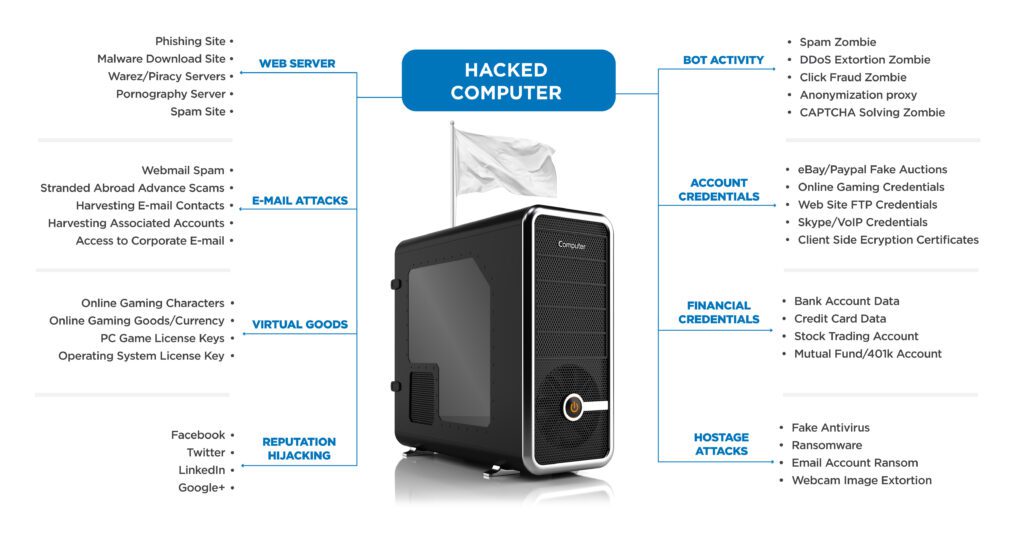
Use These Tests To Block Hackers
• White box penetration test – In a white box test, the hacker will be provided with some information ahead of time regarding the target company’s security info.
• Black box penetration test – Also known as a ‘blind’ test, this is one where the hacker is given no background information besides the name of the target company.
• Covert penetration test – Also known as a ‘double-blind’ vulnerability test, this is a situation where almost no one in the company is aware that the test is happening, including the IT and security professionals who will be responding to the attack. For covert tests, it is especially important for the hacker to have the scope and other details of the test in writing beforehand to avoid any problems with law enforcement.
• External penetration test – In an external test, the InData ethical hacker goes up against the company’s external-facing technology, such as their website and external network servers. In some cases, the hacker may not even be allowed to enter the company’s building. This can mean conducting the attack from a remote location or carrying out the test from a truck or van parked nearby.
• Internal penetration test – In an internal test, the InData ethical hacker performs the test from the company’s internal network. This kind of test is useful in determining how much damage a disgruntled employee can cause from behind the company’s firewall.
What Should Be Your Penetration Test Methodology?
Most penetration tests begin by completing an online form provided to you by your InData contact or InData ethical hacker. The form consists of multiple questions regarding what type of test you are interested in and what you would like to accomplish. The actual pen test process begins with a phase of reconnaissance, during which an InData ethical hacker spends time gathering data and information that they will use to plan their simulated attack. After that, the focus becomes gaining and maintaining access to the target system, which requires a broad set of tools.
Custom tools for attack include software designed to outline and exploit both known and unknown security vulnerabilities. There is also hardware specifically designed for pen testing, such as small inconspicuous boxes that can be plugged into a computer on the network to provide the hacker with remote access to that network. In addition, an InData ethical hacker may use social engineering techniques to find vulnerabilities. For example, sending phishing emails to company employees, or even disguising themselves as delivery or repair personnel to gain physical access to the building or restricted areas.
The InData ethical hacker wraps up the test by covering their tracks; this means removing any embedded hardware and doing everything else they can to avoid detection and leaving the target system exactly how they found it.
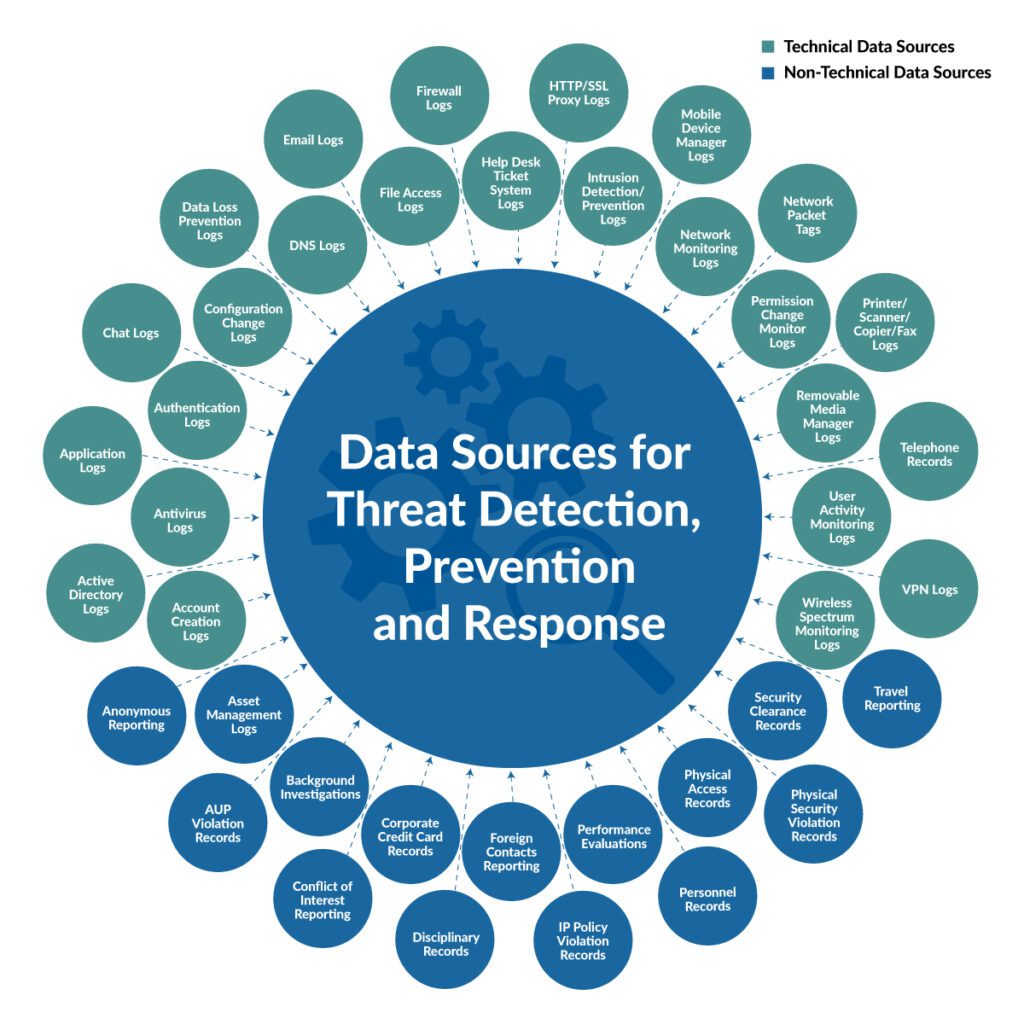
What Happens After The Penetration Test?
After completing a penetration test, the InData ethical hacker will share their findings with the target company’s IT department or executive team. This information can then be used to implement security upgrades or configuration changes to resolve any outstanding vulnerabilities discovered during the test that are deemed high risk or are preventing adherence to compliance policies. These upgrades and configuration changes can include firewall reconfigurations, updated security hardware, and possible software updates as well as tighter form validations and sanitization.
